We defend against ever-evolving cybercrime threats with advanced solutions for detection and interception, including automation, AI, and intelligent analytics.
PEACE OF MIND
Let our software engineers and analysts give you the confidence that comes from implementing the most sophisticated cybersecurity tools available.
CYBERSECURITY
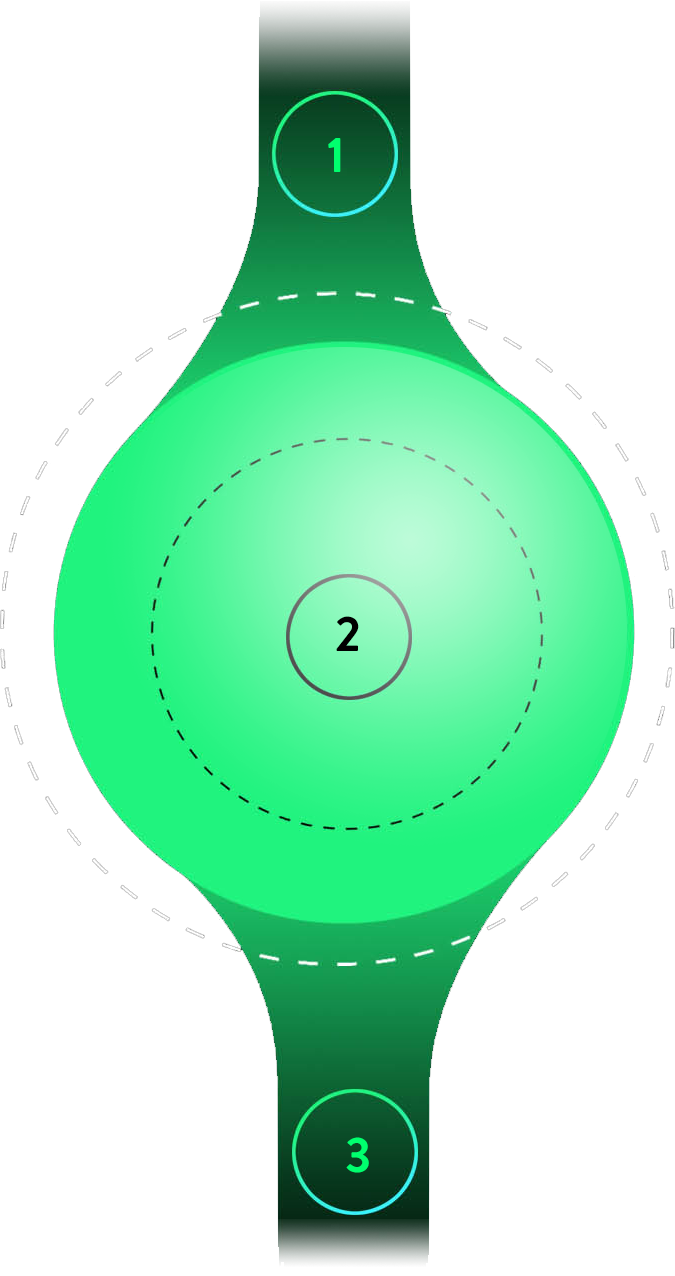
At the heart of cybersecurity software is intrusion detection, which is constantly monitoring your networks for signs of malicious activity before it happens.
1. IMPLEMENTATION
We seamlessly install, manage, and optimize your cybersecurity/intrusion detection system.
2. VULNERABILITY ASSESSMENT
We use AI’s predictive tools to determine where you’re exposed, then prescriptive analytics to recommend a course of action.
3. INCIDENT RESPONSE
We put action plans in place to swiftly mitigate any detected threats to your organization.
How can we help you with your software integration needs?
Contact Us
Copyright © 2022 Integrated Systems Consultant. All rights reserved.